So, you’ve heard about these latest, amazing techniques to get more views on YouTube. But how do they work? What is the big deal with these new-age tricks of the trade? Are they worth your while? These are just some of the things you might want to mull over.
The Basis Of Youtube Algorithm
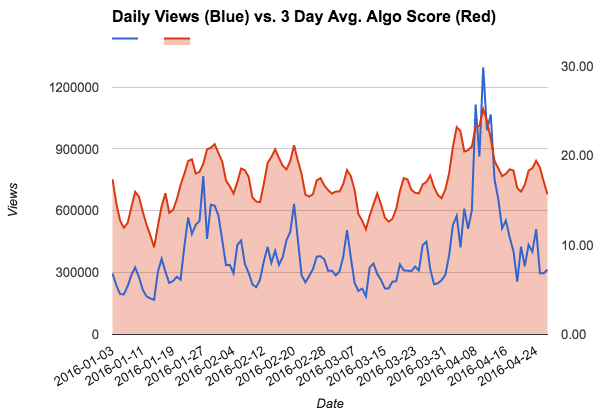
First, to really understand what all of this stuff is about, you need to understand a bit of how YouTube works.
You see, there are certain keywords, phrases, and things that search engines use to pull up the most relevant videos based on a set of standards known as the “keyword density” or “content quality.”
YouTube, unlike many other video-sharing sites, gives a lot of weight in these areas. For example, if a video has one or more keywords or keyword phrases, it’s likely to come up toward the top of any given video list.
In fact, some YouTube users actually prefer to watch videos based on such factors, so it’s important to try and get your video to the top!
The challenge then becomes to get people to watch those videos. It may seem like a hopeless endeavour.
After all, millions of people have YouTube channels, so how in the world would they ever find your video? But YouTube’s search engine, called YouTube Search, makes this whole process a lot easier than you might realize.
Use Keywords In Title and Description
With YouTube Search, you can find popular videos by searching for specific keywords.
For example, if I want to find out more information about “puppy training,” I’d use the term “puppy training”, and YouTube will pull up all of the videos that come up under that term.
From there, I’ll want to look at the videos that come up first, which is obviously going to be ones that other people have shared.
Since there are billions of videos uploaded every day, there is bound to be something that interests someone. It’s just a matter of looking for it!
Of course, even after finding a video that interests me, it’s not going to do me any good if nobody views it. There has to be an audience for the video, and YouTube Search makes it really easy to find audiences.
Just enter a broad keyword into the search bar, and you’ll see results showing up on the screen quickly. If you have an interesting video that you think would appeal to a large audience, it just needs a little help getting to the top of the rankings!
When you’re trying to get your video seen, you have to stay organized.
Stay Organized
It’s a huge world out there, and you’ll never be able to watch everything that gets uploaded. You have to remember to stay focused and only post the best videos to get you the exposure you want.
If you post anything that isn’t newsworthy or the latest in your niche, there’s a good chance that you won’t be able to get it to the top of the lists.
If you want to make sure that your video is actually viewed, you have to take some time to promote it properly.
Write Catchy Title
While the title is important, the first 100 or so words are usually what keeps people on a site. So you need to make sure that your video starts off with an attention-grabbing title that’s catchy as well as creative.
The last few tips aren’t much different than the others. Video marketing is all about using as many different ways as you can to get your video out there.
Conclusion
The more methods you use, the better chance you have of having multiple people link to your video from different websites.
This will increase the number of views fast! You indeed need a video that’s of high quality, but you don’t necessarily have to invest a lot into getting it out there.